Desktop Central SAML Integration
This document explains how to implement MonoSign with Desktop Central. It covers Single Sign-On. Before you continue, it is better to start with Desktop Central’s Single Sign-On implementation page.
View Desktop Central SSO Metadata
In order to configure the SAML key on MonoSign for Desktop Central SSO, you need to have various information provided by Desktop Central. First, navigate to Admin > SAML Authentication.
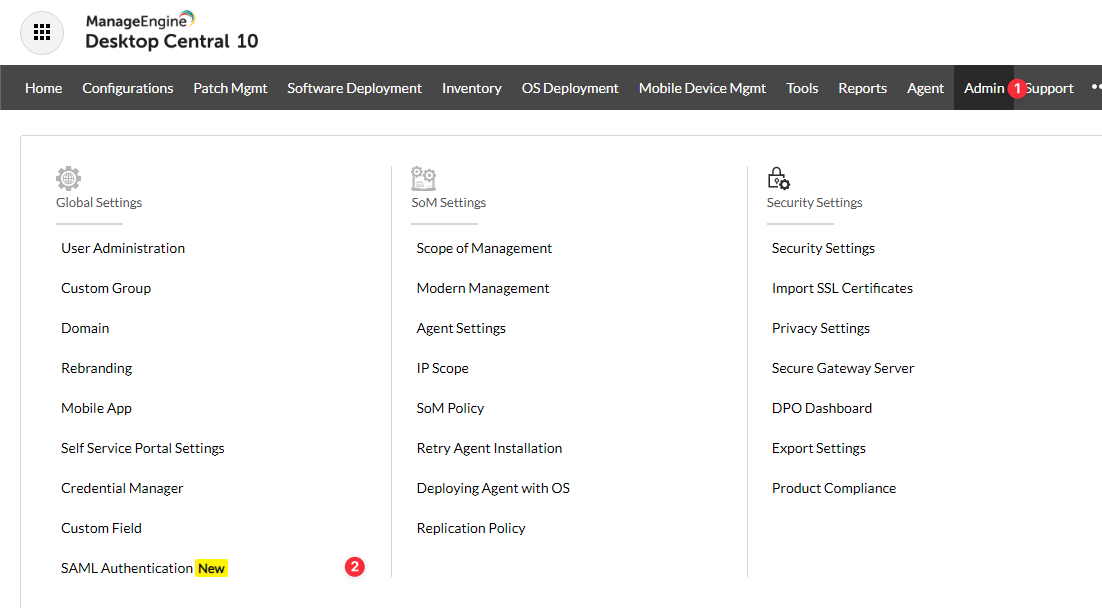
You will see Service Provider Details as follows.
For now, we will stop here on the Desktop Central side and create a MonoSign application and related SAML key by using the information provided by Desktop Central.
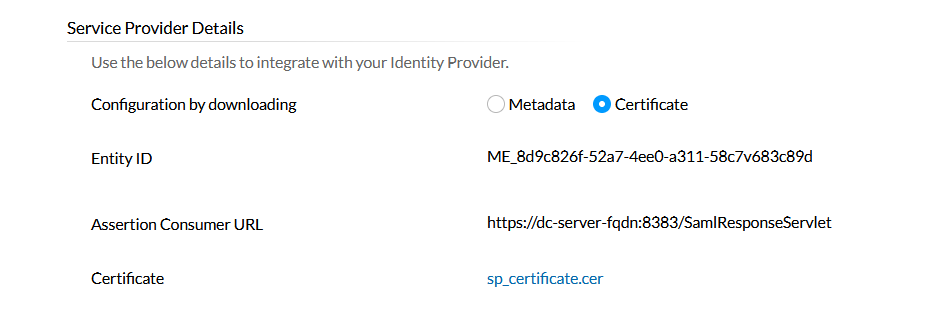
Creating an Application and Access Key on MonoSign
Create your application on MonoSign and configure your access policy. Once you create, click Keys and Add New Key to create a SAML access key.
In the opened modal, choose SAML as Key Type and switch to SAML2 Settings. Fill in the necessary fields according to the information provided by Desktop Central. Correspondings of the fields are as below.
Field | Value |
|---|---|
Assertion Consumer Url | Desktop Central Assertion Consumer Url from Service provider details |
Entity Id | Desktop Central Entity ID from Service provider details |
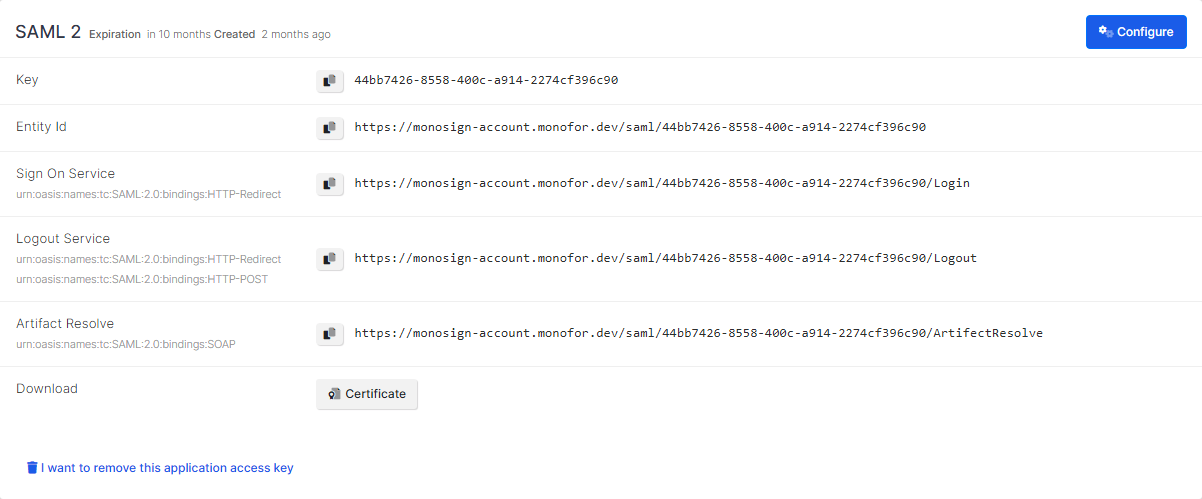
Click Save and you are gonna see your configuration for your access key as follows.
Configuration Single Sign-On for Desktop Central
We are gonna move on to where we left off on the Desktop Central SAML Authentication page which is mentioned in the first chapter. At the bottom, the Identity Provider Details form is located.
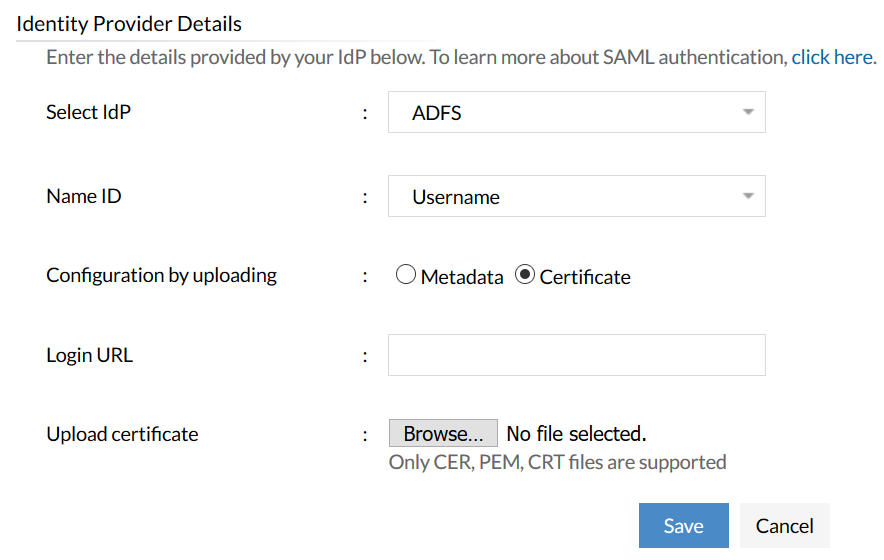
Fill in the IdP’s detail form according to the access key created on MonoSign. Correspondings of the fields are as below.
For domain users, the Username should be in this format: domain\username.
Field | Value |
|---|---|
Name ID | Attribute to uniquely identify the user who is trying to sign in |
Login URL | Sign On Service from the application SAML key |
Certificate | The certificate issued to access key - can be downloadable from the key detail. |
For SAML, provisioning method is manual which means the user must be present both in the IdP and Desktop Central.