FortiGate Admin Login SAML Integration
This document explains how to implement Monosign with FortiGate Firewall Admin login. It covers Single Sign-On. Before you continue, it is better to start with FortiGate's Single Sign-On this page.
To be able to use SAML as an authentication method you need to have FortiOS@6.4 or above.
📑 Instructions
This documentation contains 4 main steps for integration.
Creating an Application on Monosign
Configuration Single Sign-On for FortiGate
Assign a user to the FortiGate application
Sign In Test
Optional Settings on Fortigate
1- Creating an Application on Monosign
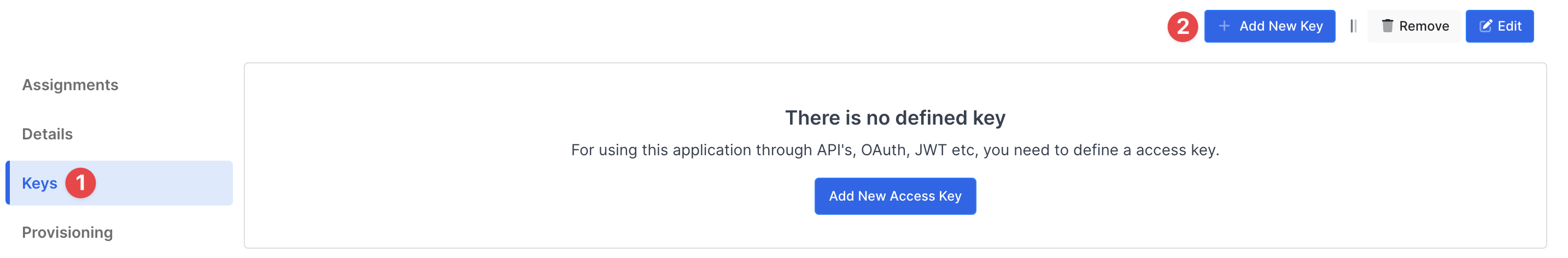
Create application on Monosign and configure your access policy. Once you create, click “Keys” and add a new Access Key for SAML Key for access.
This information will be necessary during the configuration of the FortiGate application.
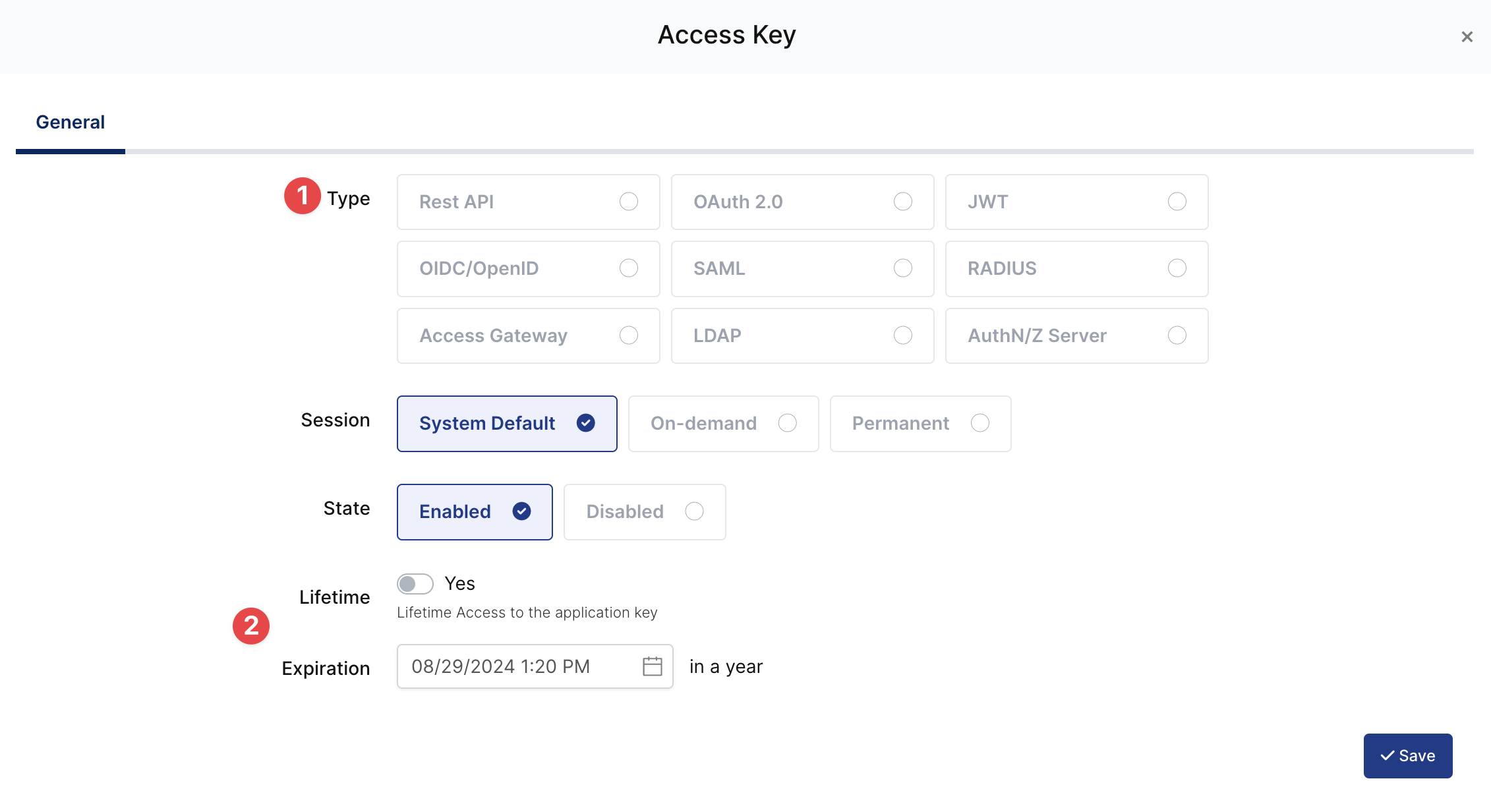
Property | Value | Options |
|---|---|---|
Key Type | SAML | Rest API, OAuth 2.0, JWT, OIDC/OpenID, SAML, RADIUS, Access Gateway, LDAP, AuthN/Z Server |
Expiration | Lifetime | Lifetime or Specific Date/Time - By Default Lifetime is Enabled. |
Configuration details for the FortiGate application are provided as follows:
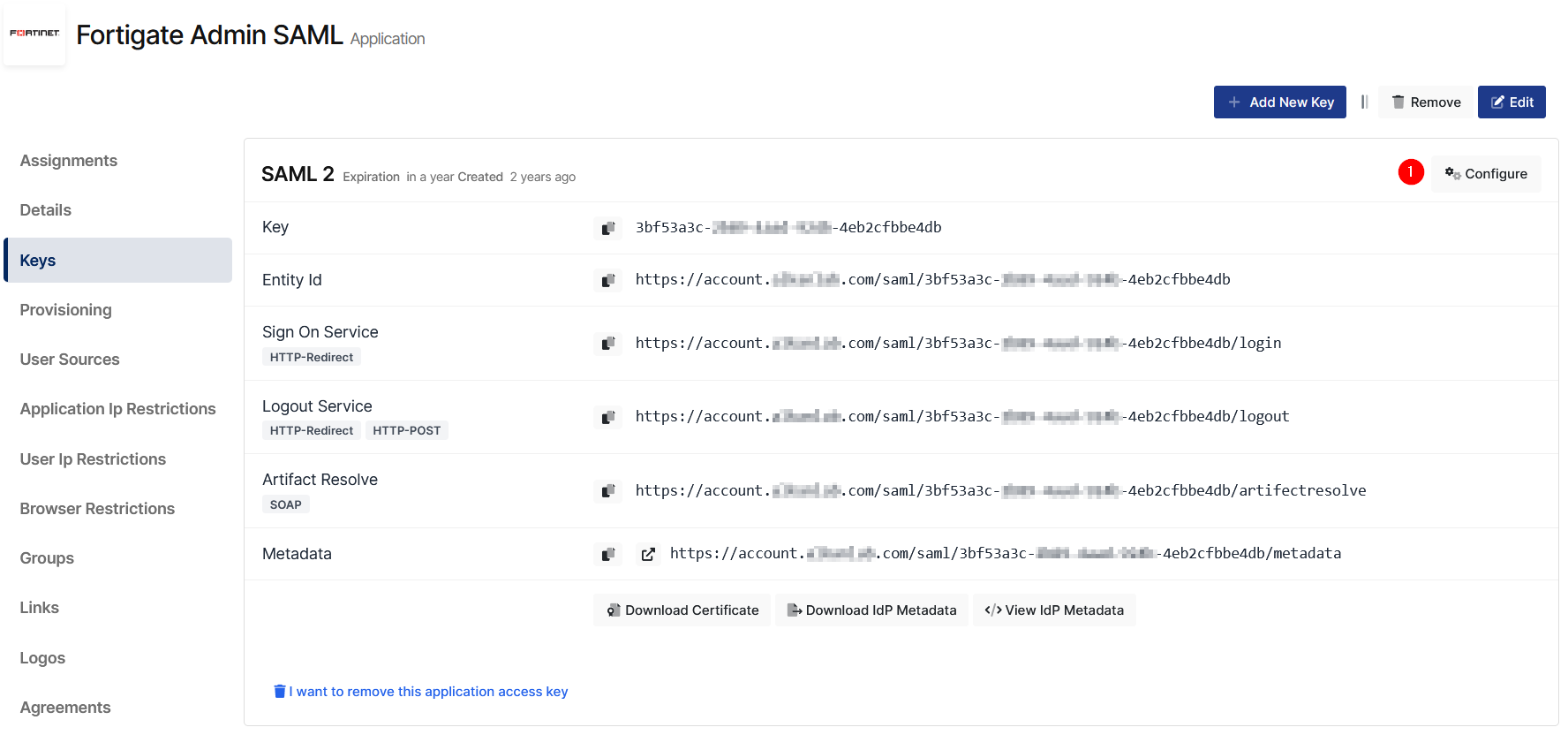
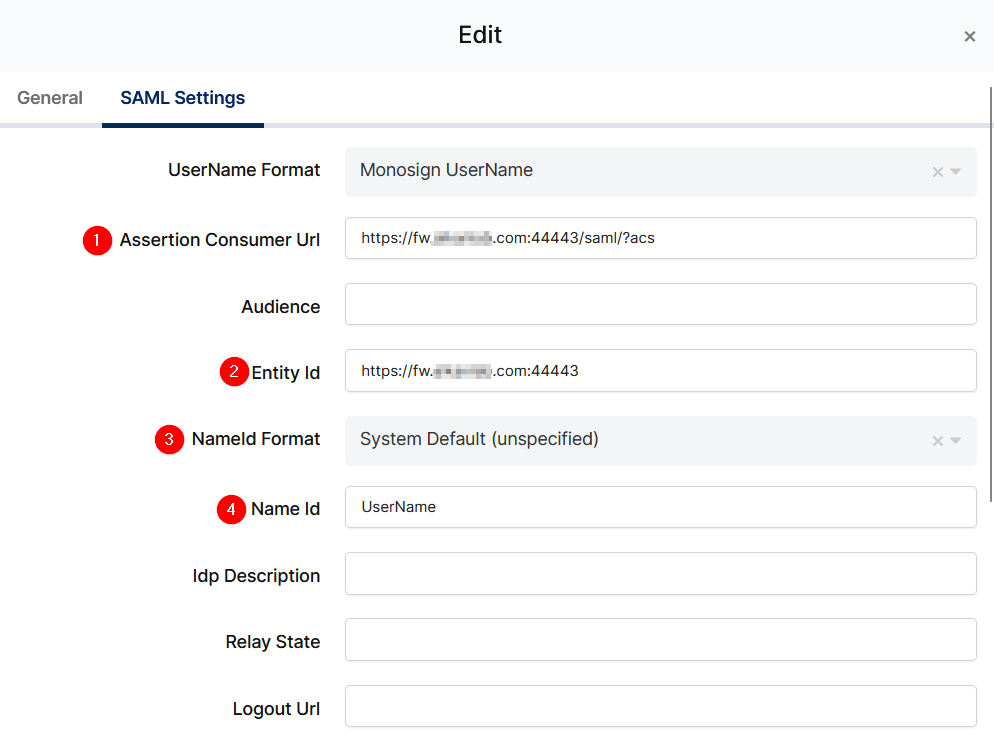
Change ACS(Assertion Consumer Url), Entity Id, NameId Format, Name Id and Extra Attributes.
Property | Value |
|---|---|
Assertion Consumer Url |
|
Entity Id |
|
NameId Format |
|
Name Id |
|
Extra Attribute |
|
To ensure that the application has access to user groups, follow these steps:
If the application hasn't been configured yet, click the “Edit” option for the application.
In the application settings, navigate to the “Source, Provider, and Profile” tab.
Configure the “User Access Type“ and “User Group Access Type” as “Only Assigned Users.”
Configuring this setting will allow the application to access by user groups when users sign in.

Property | Description | Options |
|---|---|---|
User Access Type | Defines which Users will access to this application. | Only Assigned Users |
User Group Access Type | Defines application’s user group access | Only Assigned Users |
Profile Access Type | Defines Application’s user’s profile access | Restricted - Only restricted user profile attributes |
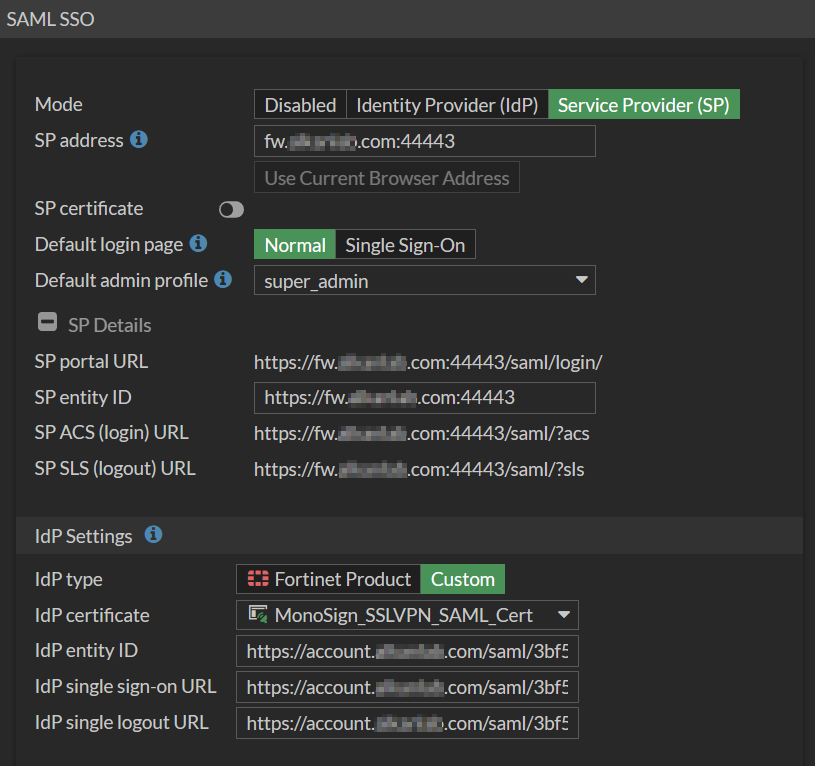
2- Configuration Single Sign-On for FortiGate
As it highlighted at the beginning of document, please check out the FortiGate’s SSO configuration page first.
Please add your SAML settings to the application. The following information is needed for your configuration.
Property | Value |
|---|---|
server-address |
|
default-profile |
|
entity-id |
|
idp-entity-id |
|
idp-single-sign-on-url |
|
idp-single-logout-url |
|
idp-cert |
|
Before continue please download Monosign IdP certificate from the application key details.
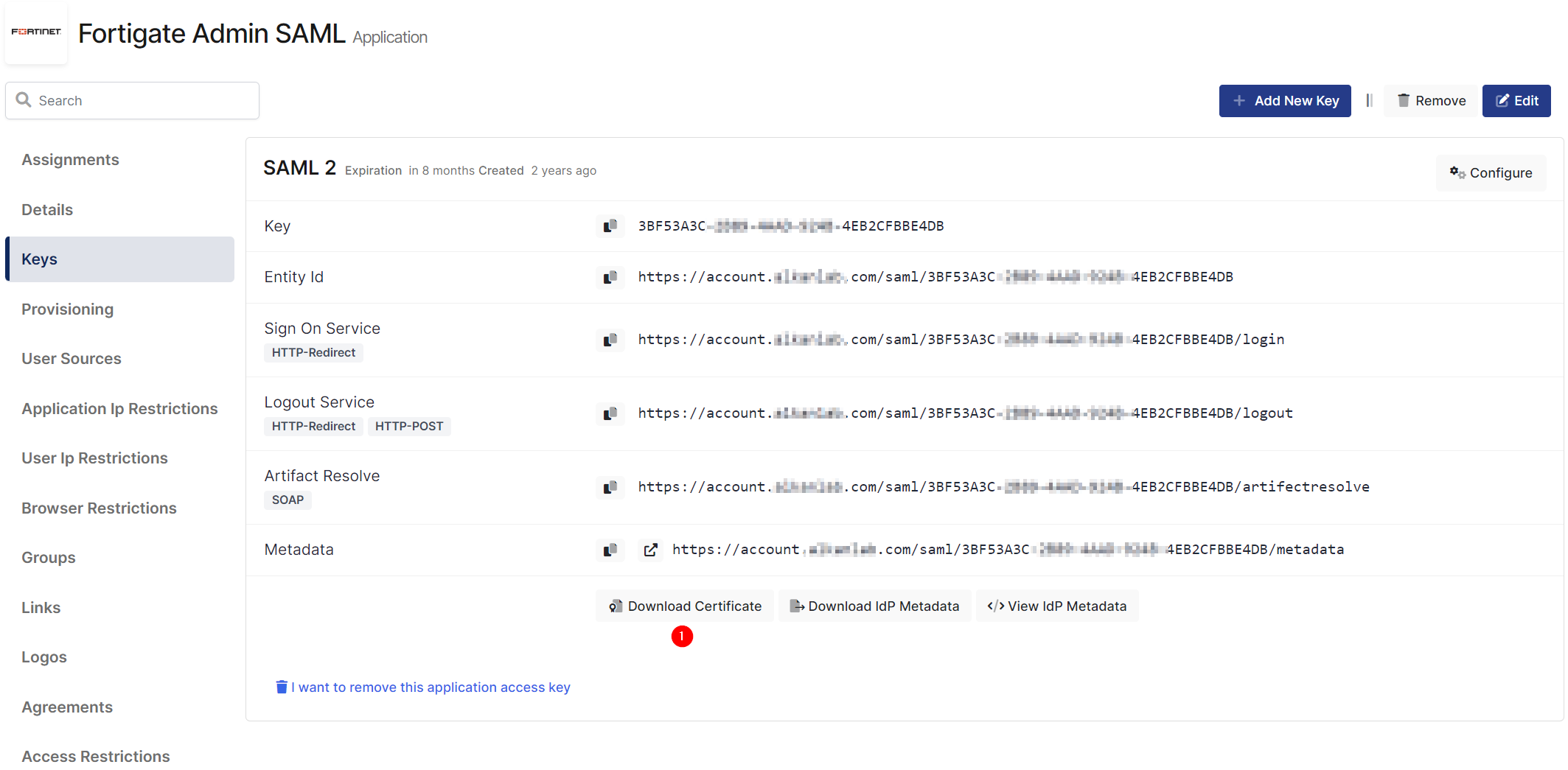
From CLI
Connect your FortiGate firewall via command line and run below commands.
config system saml
set status enable
set server-address "<FW_IP_FQDN:PORT>"
set default-profile "super_admin"
set entity-id "https://<FW_IP_FQDN:PORT>"
set idp-entity-id "https://account.monofor.com/saml/3f98a9d6-cf28-4cfd-8427-f4506b33ffcb"
set idp-single-sign-on-url "https://account.monofor.com/saml/3f98a9d6-cf28-4cfd-8427-f4506b33ffcb/Login"
set idp-single-logout-url "https://account.monofor.com/saml/3f98a9d6-cf28-4cfd-8427-f4506b33ffcb/Logout"
set idp-cert "Monosign_SAML_Cert"
endFrom Web GUI
From FortiOS 6.2 to 7, Go to Security Fabric → Settings → SAML single Sign-On
After FortiOS 7 Go to Security Fabric → Fabric Connectors and Edit Security Fabric Setup. Click Single Sign-On Settings
Now, go back to Monosign and give access to your users and try login.
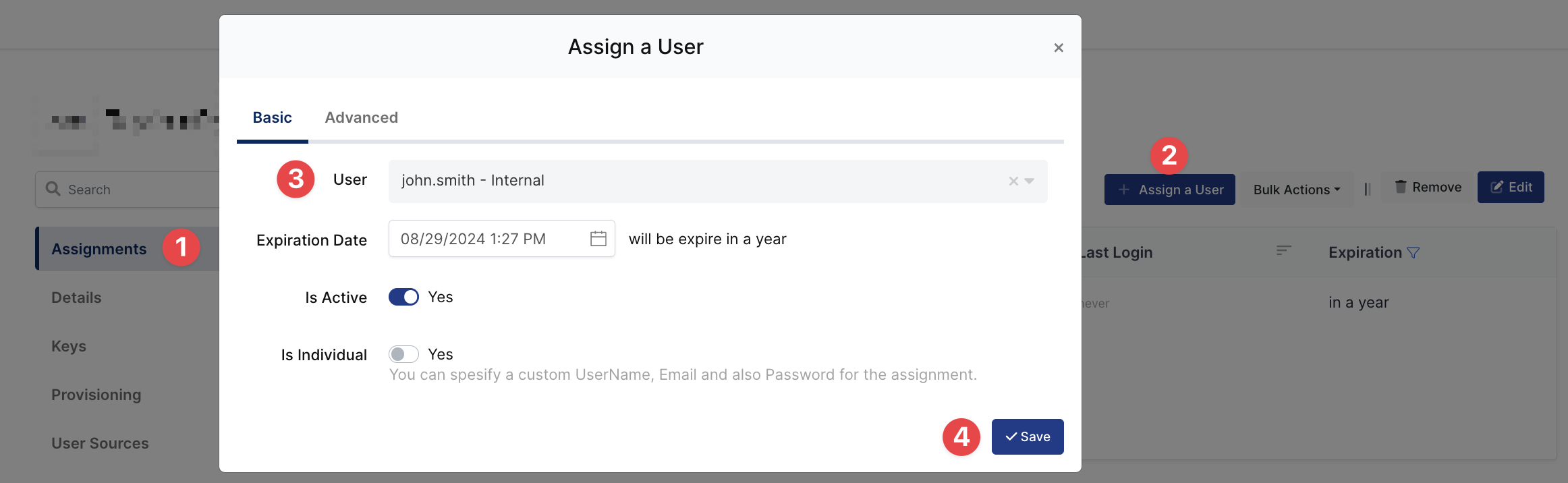
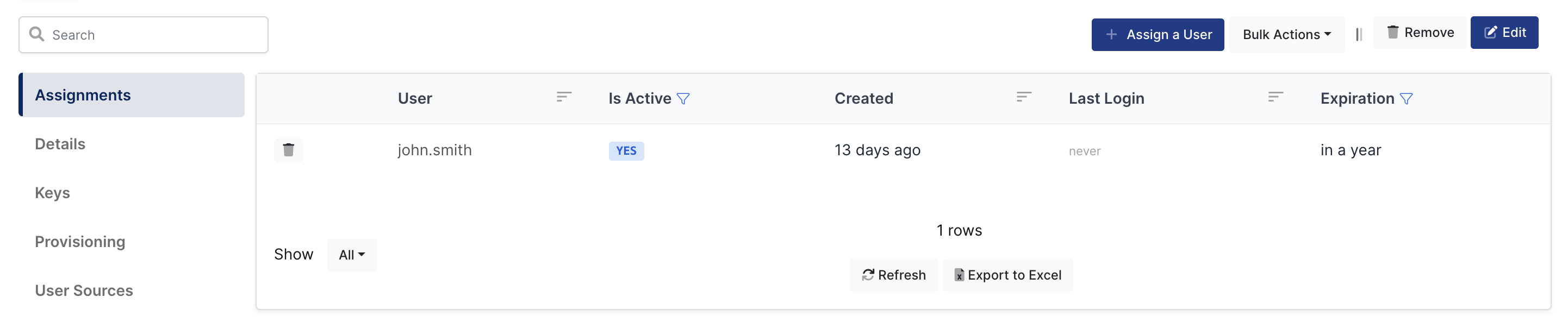
3- Assign a user to the FortiGate application
Please follow below instructions on how to assign a user to the FortiGate application. In this example john.smith will assign to the application access.
4- Sign In Test
Now try login. Navigate to the FortiGate application. Click Sign in with Security Fabric.
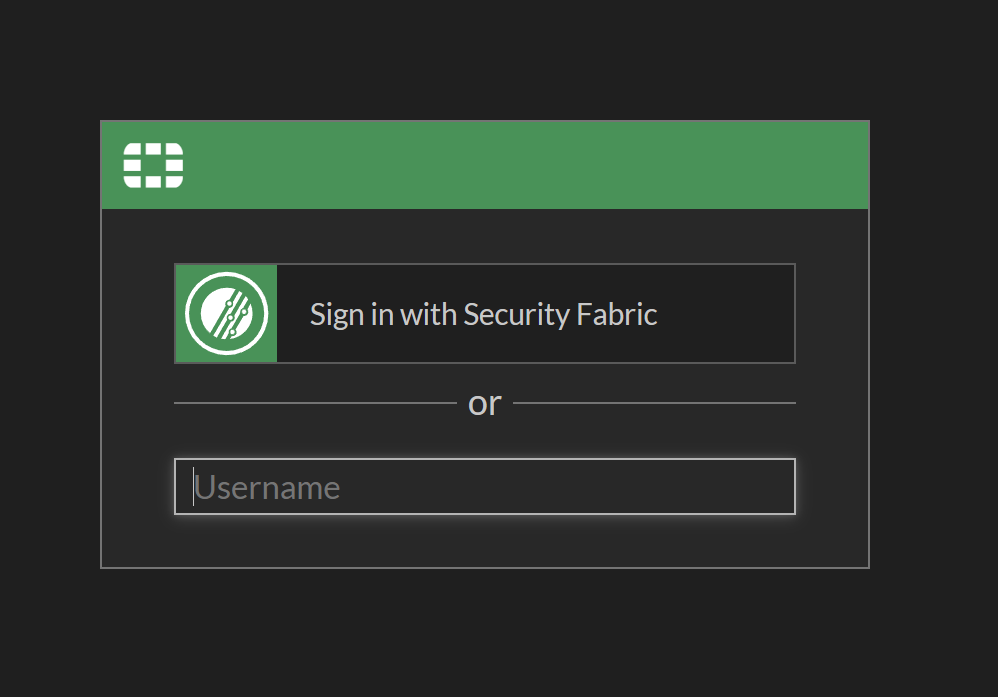
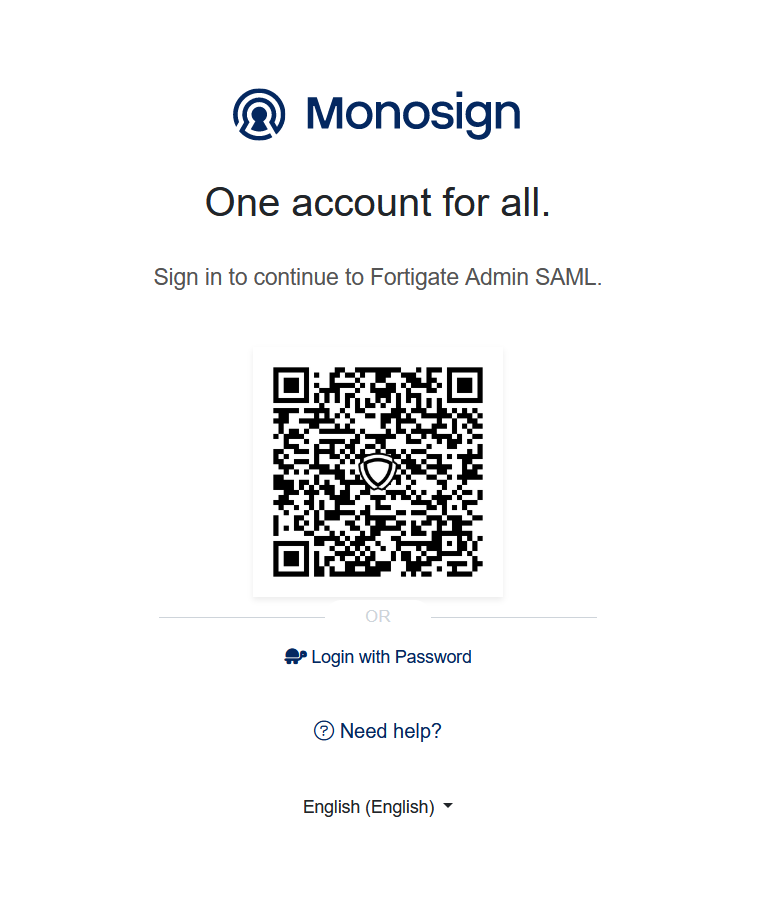
If everything is well configured, the page will be redirected to Monosign’s login page. It can be log in passwordless with QR code or type username and password.
After that FortiGate warn assigned user has been created on the firewall.
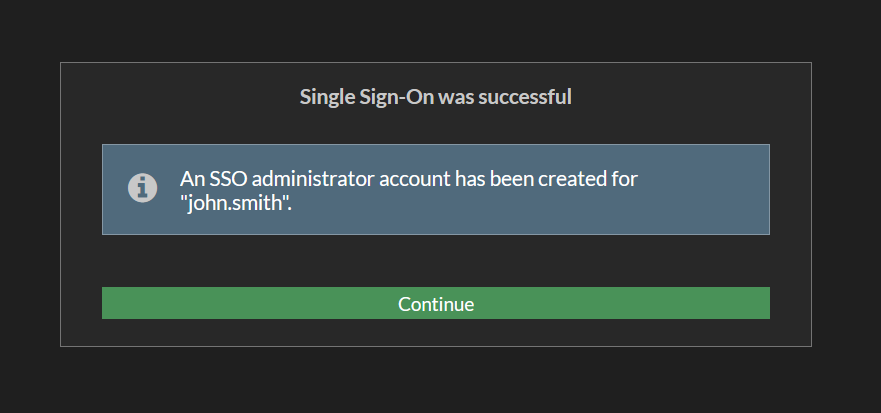
When the user logged in, the page will be redirected to the FortiGate Admin page. It can be verified right top of the page new user is logged-in with SSO.

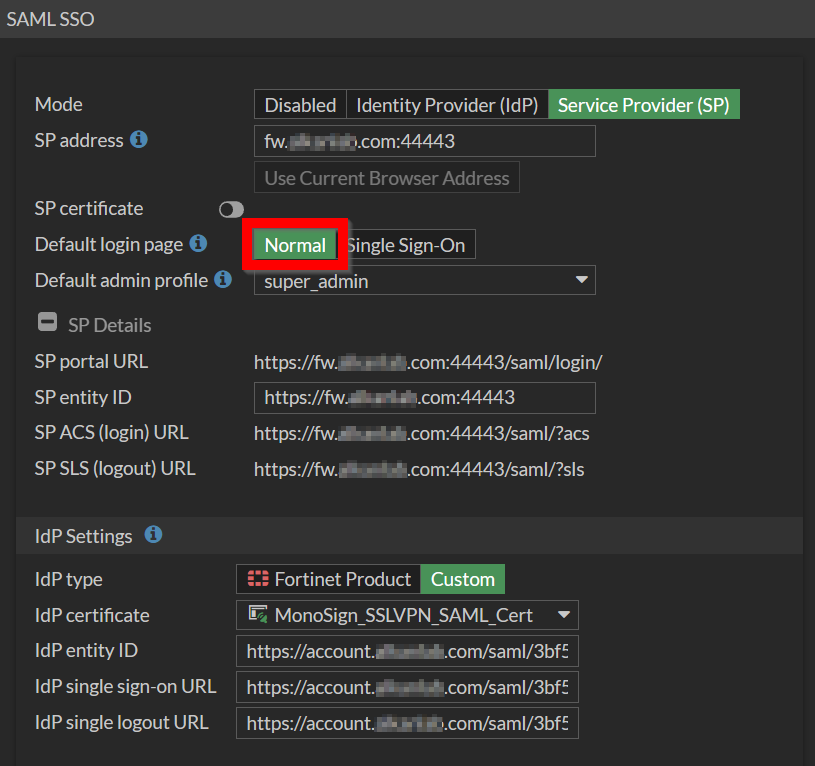
5- Optional Settings on FortiGate
By default FortiGate is using local and SSO login in the same login page. It can be disable local login please follow below steps.
CLI
Set Default-Login Page to SSO
config system saml
set default-login-page sso
endRevert back to login page from SSO to Normal
config system saml
set default-login-page normal
endWeb UI
Set Default-Login Page to SSO
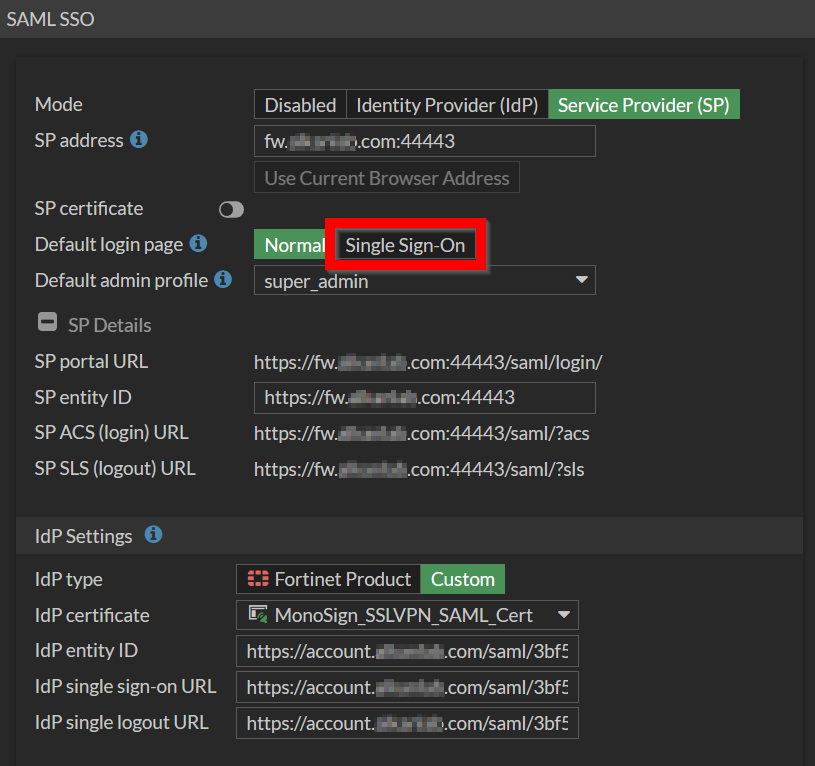
Revert back to login page from SSO to Normal