LDAP - Generic - User and Profile Sync
This document will help you to add a new LDAP User Source rather than an Active Directory source.
📘 Instructions
This documentation will contain two main steps.
Adding a User Source
Configuring the Settings
Active Directory and LDAP settings are different. Please consider to use LDAP settings rather than Active Directory settings. On MonoSign for version 2023.01, we need to use following configuration for LDAP.
1. Adding a User Source
Create your User Source on MonoSign and select the type Active Directory / LDAP by reading the documentation.
2. Configuring the Settings
MonoSign has different LDAP options. Click Settings to configure details.
When you have your page, select a different option than Microsoft Active Directory. Such as OpenLDAP, Oracle Unified Directory, or find your provider.
Example configurations
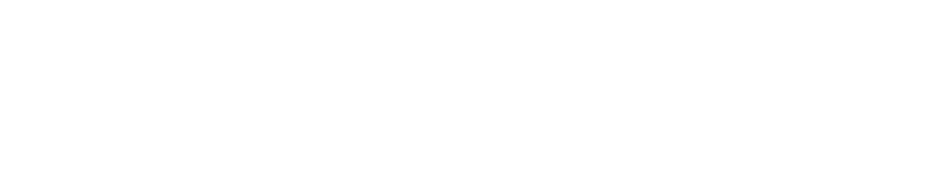
After you have finished it, please use the following options to configure it.
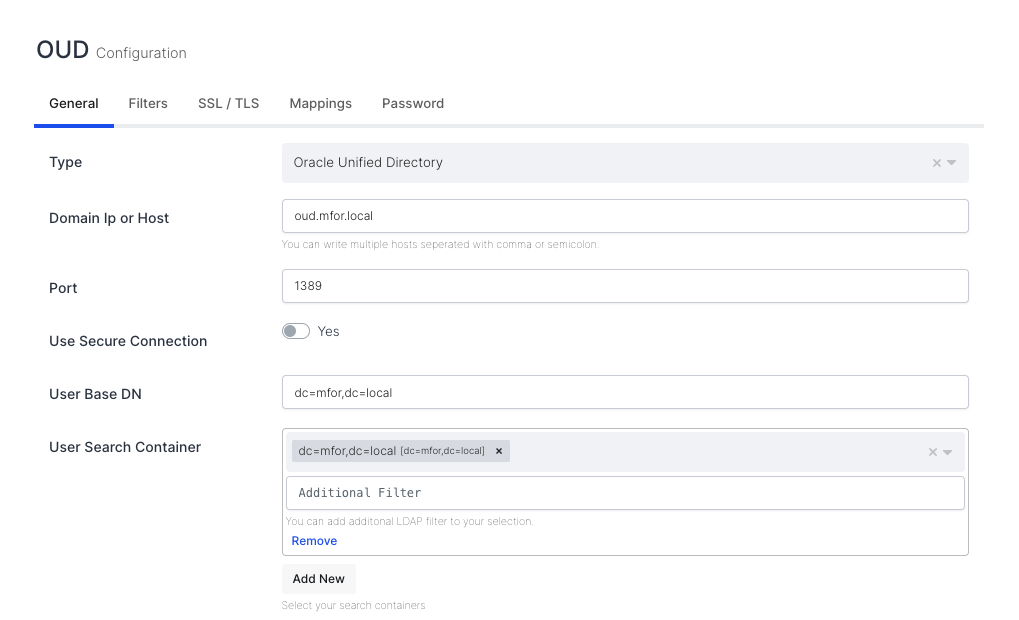
Domain Username and Password
Setting | Value | Example(s) |
|---|---|---|
Domain Ip or Host | Type your DNS or IP address | oud.mfor.local |
Port | Your LDAP Port |
|
Use Secure Connection | Yes or No depending your settings |
|
User Base DN | Your users Base DN |
|
User Search Container | Your can use multiple search container for your users store. |
|
Group Base DN | Your groups Base DN |
|
Group Search Container | Your can use multiple search container for your groups store. |
|
Domain Name | Your domain name |
|
Domain UserName | Username for authentication |
|
Domain Password | Password of the Domain UserName |
|
Sample UserName | Username if you want healtcheck |
|
Sample Password | Password of the Sample UserName |
|
Use BaseDN for Authentication | Should be Yes for LDAP |
|
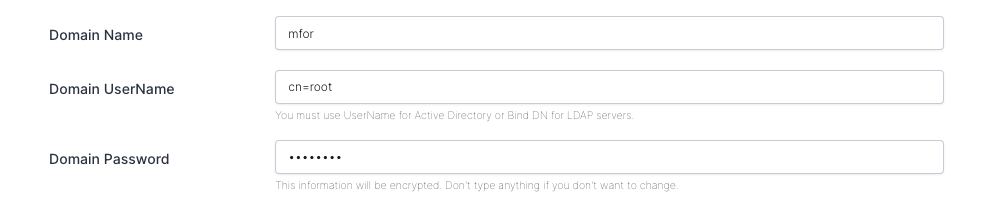
These settings are enough for the first connection but not enough for filters and more. Let’s continue. The following settings are also required for Filters.
Domain Ip or Host field allows for multiple domains to be configured. You can enter domains by separating them with commas.
Manages hostnames with connection errors in MonoSign via blacklist. If I have only one hostname and encounter a connection error, it is added to the blacklist immediately and will not be removed until the next restart. If there is multiple hostnames, hostname is added to blacklist for 10 minutes and during this interval the other hostnames will be used.
Settings | Value |
|---|---|
User Search Filter |
|
Group Search Filter |
|
Text Filter |
|
Basic Text Filter |
|
Id Filter |
If you are using both uid and cn name for user, you need to change it with;
For Oracle Unified Directory
|
You can also use your filter settings if you know what to do. You can also use mappings to map your attributes to your MonoSign Profile. On the left side, your LDAP attribute name; on the right side, it should be your Profile Property Name (without spaces).
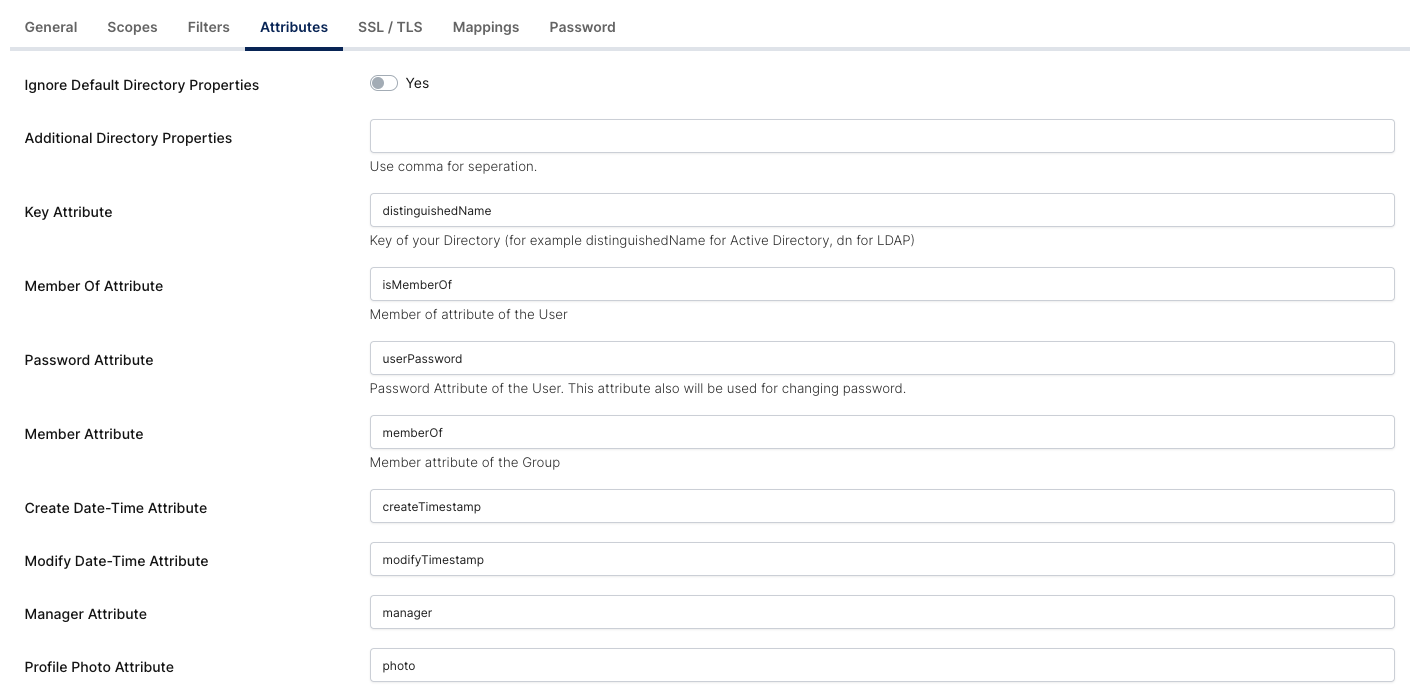
Modify Attributes for LDAP
In Oracle Unified Directory, Modify Date and Create Date attributes differ from Active Directory. For example, in Active Directory, these attributes are whenChanged and whenCreated. And also, you need to change Password Attribute for Oracle and may also some directories too.
Property | Value | Example |
|---|---|---|
Create Date-Time Attribute |
| 20230223093716Z |
Modify Date-Time Attribute |
| 20230224231708Z |
Password Attribute |
|
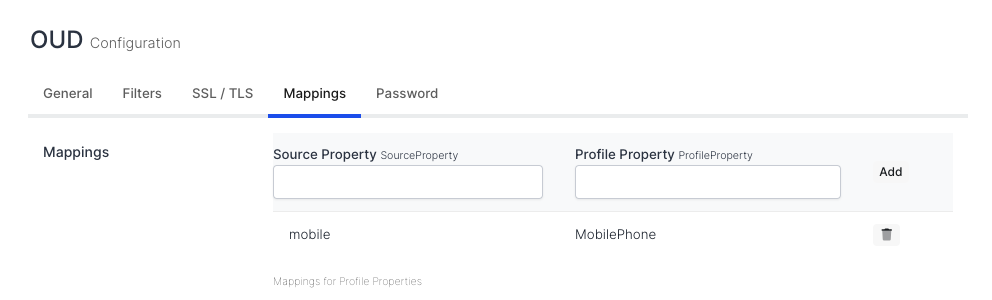
Example Mappings
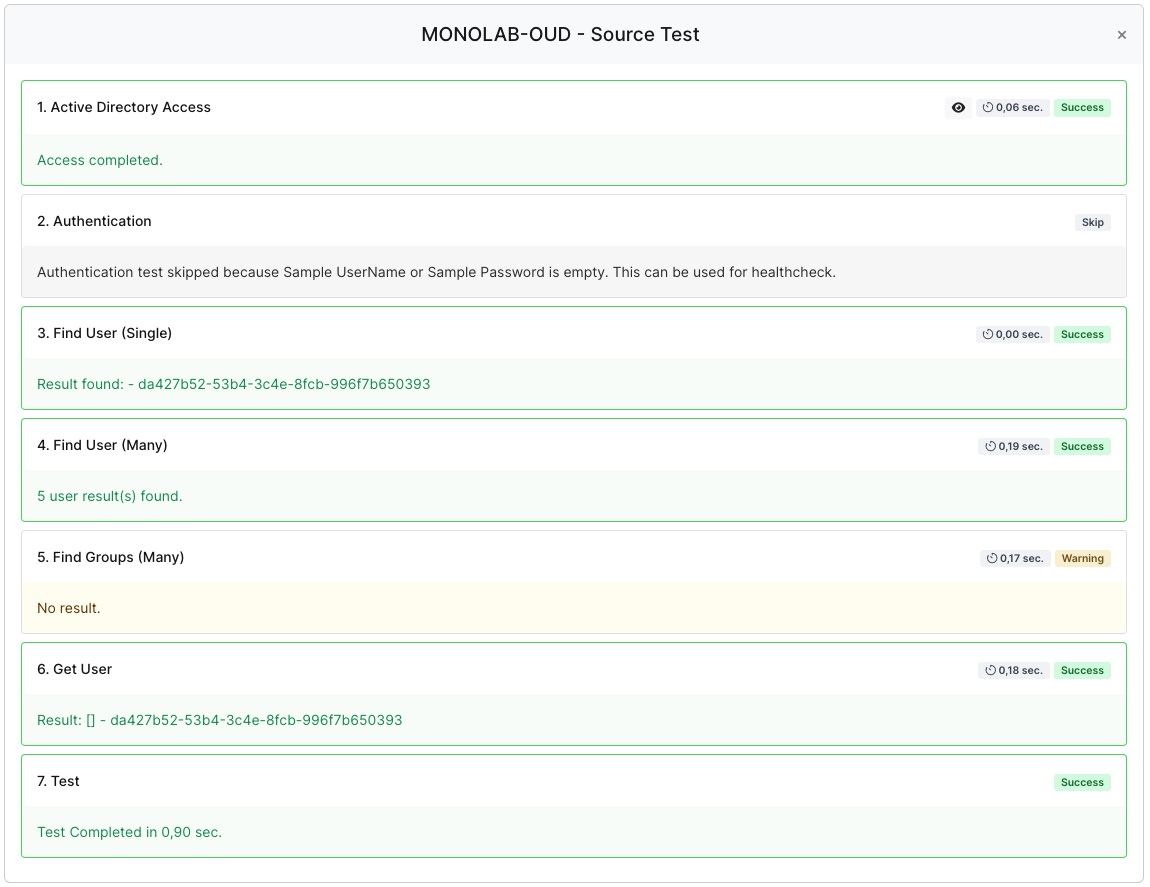
When you click Test, you are going to see the following UI. I don’t have any Groups in my directory. That’s why one of the items seems to be different in color.
Following settings are for Oracle Unified Directory (OUD)
If you use a service user configured with ACI (Access Control Instructions), you need to specify the following options for that user.
Attribute | Value | Description |
|---|---|---|
|
| Allow unindexed search |
|
| Pagination size of each page for search |
| Time limit of the idle connection | |
|
| Maximum size of your user count or upper number of that size. |
| Time limit of the search request |
If you want to set these settings with ldapmodify, execute the following command with ldap ldif file.
Shell Command
ldapmodify -h hostname -p 1389 -D "cn=Directory Manager" -w $MONOFOR_OUD_PASSWORD -f ./target-aci.ldifLDIF File (target-aci.ldif)
dn: o=monofor
changetype: modify
add: aci
aci: (targetattr="*")(target="ldap:///o=monofor")(version 3.0; acl "Allow read access to specific OU"; allow (read, write, search, compare) userdn="ldap:///uid=search.user,ou=service-users,o=monofor";)Explanation of the LDIF file
dn is the target definition
changetype is the action of ldapmodify
add is attribute
aci is the definition of Access Control Instructions
Exploration of aci
(targetattr="*") are attributes that you need to specify star means all attributes
(target="ldap:///o=monofor") is the ou or target level of your aci
(version 3.0; acl "Allow read access to specific OU"; allow (read, write, search, compare) userdn="ldap:///uid=search.user,ou=service-users,o=monofor";)
allow is the definition of access. For example, we will give our service user permission to read, write, search, and compare.
userdn is the target user that we will give permission.
If you are dealing with the following error, your limit settings are not set correctly.
This search operation has sent the maximum of 5 entries to the client
You can also set configurations through ds-config such following example;
./dsconfig.bat --trustAll -h hostname-of-oud -p 4444 -D "cn=directory manager" -j C:\Oracle\Configuration\manager-password.txt -X set-global-configuration-prop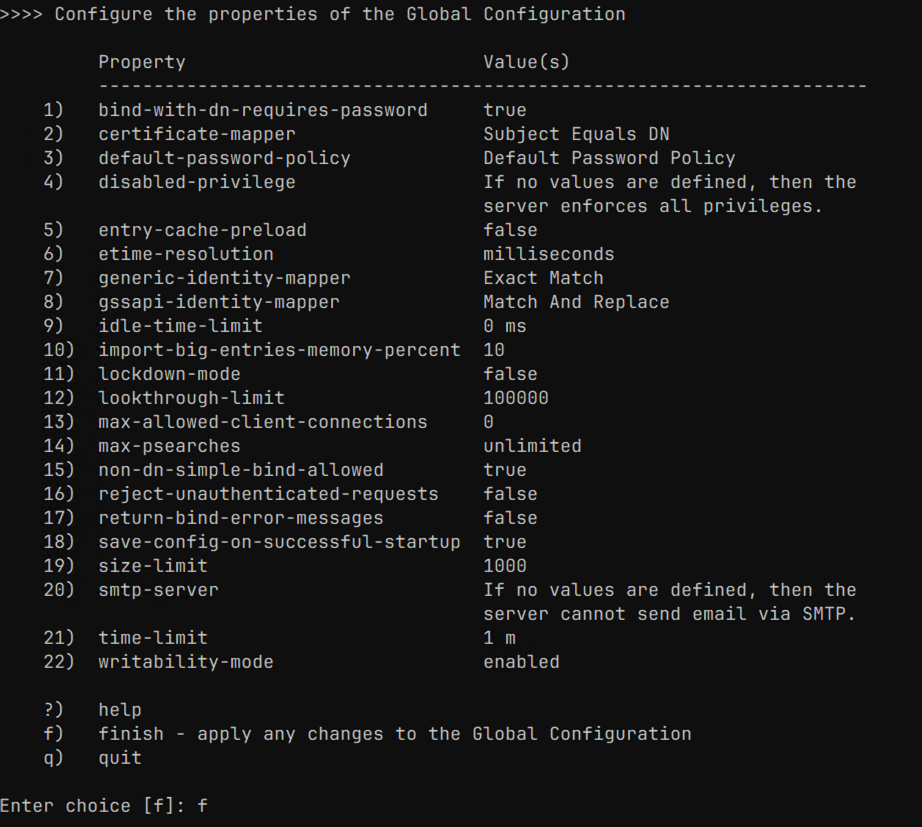
Oracle Unified Directory DS Config CLI
These settings are enough for your environment. If you want more, please talk to your support.